Protocols are set of rules which govern every possible
communication over a network. These protocols describe the movement of
data between the source and destination or the internet. They also offer
simple naming and addressing schemes
Protocol Layering
- The services that a layer offers to the layer above is so a called service model of a layer. Each layer provides its service by
(1) performing certain actions within that layer and by (2) using the services of the layer directly below it
- A protocol layer can be implemented in software, in hardware, or in a combination of the two.
- layering provides a structured way to discuss system components.
- Modularity makes it easier to update system components.
Drawback
- One layer may duplicate lower-layer functionality. For example, many protocol stacks provide error recovery on both a per-link basis and an end-to-end basis.
- Functionality at one layer may need information (for example, a time-stamp value) that is present only in another layer; this violates the goal of separation of layers.
When taken together, the protocols of the various layers are called the protocol stack. The Internet protocol stack consists of five layers & OSI (Open Systems Interconnection) Model has 7 layers.
![Chapter 1. Computer Networks and the Internet [1.5 Protocol Layers and Their Service Models] - 知乎](https://pic1.zhimg.com/v2-8bc4b856673fca96090a5a12fd9ee3a8_b.jpg)
OSI Model
- The Open Systems Interconnection (OSI) model describes seven layers that computer systems use to communicate over a network.
- It was the first standard model for network communications, adopted by all major computer and telecommunication companies in the early 1980s
- The modern Internet is not based on OSI, but on the simpler TCP/IP model.
- However, the OSI 7-layer model is still widely used, as it helps visualize and communicate how networks operate, and helps isolate and troubleshoot networking problems.
7. Application Layer
- The application layer is used by end-user software such as web browsers and email clients.
- It provides protocols that allow software to send and receive information and present meaningful data to users.
- But it should be made clear that client software applications are not
part of the application layer; rather the application layer is
responsible for the protocols and data manipulation that the software
relies on to present meaningful data to the user.
- A few examples of application layer protocols are the Hypertext Transfer Protocol (HTTP), File Transfer Protocol (FTP), Post Office Protocol (POP), Simple Mail Transfer Protocol (SMTP), and Domain Name System (DNS).
6. Presentation Layer
- This layer is primarily responsible for preparing data so that it can be used by the application layer; in other words, layer 6 makes the data presentable for applications to consume.
- The presentation layer is responsible for translation, encryption, and compression of data.
- The presentation layer takes any data transmitted by the application layer and prepares it for transmission over the session layer.
5. Session Layer
- This is the layer responsible for opening and closing communication between the two devices.
- The time between when the communication is opened and closed is known as the session.
- The session layer ensures that the session stays open long enough to transfer all the data being exchanged, and then promptly closes the session in order to avoid wasting resources.
- The session layer also synchronizes data transfer with checkpoints, i.e. if the session is interrupted, devices can resume data transfer from the last checkpoint..
For example, if a 100 megabyte file is being transferred, the session layer could set a checkpoint every 5 megabytes. In the case of a disconnect or a crash after 52 megabytes have been transferred, the session could be resumed from the last checkpoint, meaning only 50 more megabytes of data need to be transferred. Without the checkpoints, the entire transfer would have to begin again from scratch.
4. Transport Layer
- Responsible for end-to-end communication between the two devices.
- This includes taking data from the session layer and breaking it up into chunks called segments before sending it to layer 3(Network Layer).
- The transport layer on the receiving device is responsible for reassembling the segments into data the session layer can consume.
- The transport layer is also responsible for flow control and error control.
- Flow control determines an optimal speed of transmission to ensure that a sender with a fast connection doesn’t overwhelm a receiver with a slow connection.
- The transport layer performs error control on the receiving end by ensuring that the data received is complete, and requesting a retransmission if it isn’t.
3. Network Layer
- The network layer is responsible for facilitating data transfer between two different networks.
- If the two devices communicating are on the same network, then the network layer is unnecessary.
- The network layer breaks up segments from the transport layer into smaller units, called packets on the sender’s device, and reassembling these packets on the receiving device.
- The network layer also finds the best physical path for the data to reach its destination; this is known as routing.

2. Data Link Layer
- The data link layer is very similar to the network layer, except the data link layer facilitates data transfer between two devices on the SAME network.
- The data link layer takes packets from the network layer and breaks them into smaller pieces called frames.
- Like the network layer, the data link layer is also responsible for flow control and error control in intra-network communication (The transport layer only does flow control and error control for inter-network communications)..
- This layer is composed of two parts—Logical Link Control (LLC), which identifies network protocols, performs error checking and synchronizes frames, and Media Access Control (MAC) which uses MAC addresses to connect devices and define permissions to transmit and receive data.
1. Physical Layer
- This layer includes the physical equipment involved in the data transfer, such as the cables and switches.
- This is also the layer where the data gets converted into a bit stream, which is a string of 1s and 0s.
- The physical layer of both devices must also agree on a signal convention so that the 1s can be distinguished from the 0s on both devices.
- It defines the connector, the electrical cable or wireless technology connecting the devices, and is responsible for transmission of the raw data, which is simply a series of 0s and 1s, while taking care of bit rate control.
Advantages of OSI Model
- Determine the required hardware and software to build their network.
- Understand and communicate the process followed by components communicating across a network.
- Perform troubleshooting, by identifying which network layer is causing an issue and focusing efforts on that layer.
How data flows through the OSI Model
In order for human-readable information to be transferred over a network from one device to another, the data must travel down the seven layers of the OSI Model on the sending device and then travel up the seven layers on the receiving end.
For example: Mr. Cooper wants to send Ms. Palmer an email. Mr. Cooper composes his message in an email application on his laptop and then hits ‘send’. His email application will pass his email message over to the application layer, which will pick a protocol (SMTP) and pass the data along to the presentation layer. The presentation layer will then compress the data and then it will hit the session layer, which will initialize the communication session.
The data will then hit the sender’s transportation layer where it will be segmented, then those segments will be broken up into packets at the network layer, which will be broken down even further into frames at the data link layer. The data link layer will then deliver those frames to the physical layer, which will convert the data into a bitstream of 1s and 0s and send it through a physical medium, such as a cable.
Once Ms. Palmer’s computer receives the bit stream through a physical medium (such as her wifi), the data will flow through the same series of layers on her device, but in the opposite order. First the physical layer will convert the bitstream from 1s and 0s into frames that get passed to the data link layer. The data link layer will then reassemble the frames into packets for the network layer. The network layer will then make segments out of the packets for the transport layer, which will reassemble the segments into one piece of data.
The data will then flow into the receiver's session layer, which will pass the data along to the presentation layer and then end the communication session. The presentation layer will then remove the compression and pass the raw data up to the application layer. The application layer will then feed the human-readable data along to Ms. Palmer’s email software, which will allow her to read Mr. Cooper’s email on her laptop screen.
TCP/IP Model
- TCP/IP means Transmission Control Protocol and Internet Protocol.
- It is the network model used in the current Internet architecture as well.
- The entire IP suite -- a set of rules and procedures -- is commonly referred to as TCP/IP.
- TCP and IP are the two main protocols, though others are included in the suite.
- The TCP/IP protocol suite functions as an abstraction layer between internet applications and the routing and switching fabric.
Layers in TCP/IP Model
The TCP/IP Model has four layers:
1. Physical Layer and data link layer – combined known as host-to-network layer
2. Network layer
3. Transport
4. Application
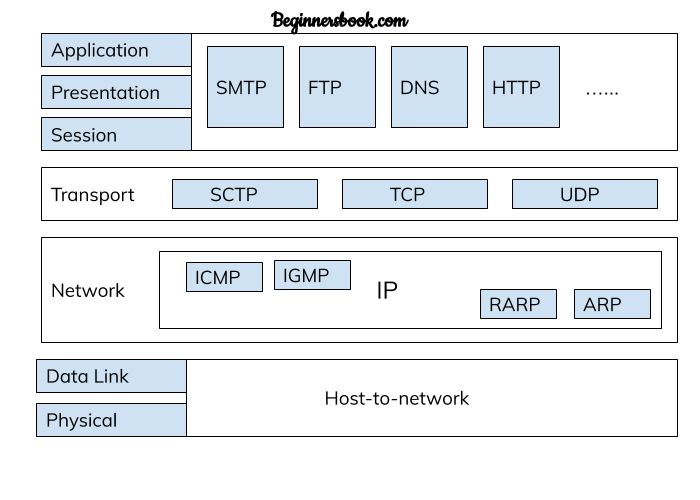
1. Physical and Data Link Layer
- Physical and Data Link Layers in TCP/IP model does not define any protocols, they support all the standard protocols.
- They are combined known as host-to-network layer.
- A network in TCP/IP internetwork can be LAN or WAN.
2. Network Layer
- In the network layer, the TCP/IP model supports internet working protocol in short known as IP.
- The IP uses four protocols internally: ARP, RARP, ICMP & IGMP.
3. Transport Layer
- Transport layer in TCP/Model can be represented by three protocols: Transmission control protocol (TCP), User data gram protocol (UDP) and Stream Control Transmission Protocol (SCTP).
- These three protocols in transport layer are responsible for delivery of messages from one process to another.
- The SCTP protocol was later introduced to meet the needs of newer applications.
4. Application Layer
- This is the top most layer of TCP/IP model.
- It is used for interaction between user and application.
- There are several protocols used by the application layer for user interaction such as: HTTP, SNMP, SMTP, DNS, TELNET, FTP etc.
Internet Architecture
Network architecture is the design of a computer network. It is a framework for the specification of a network's physical components and their functional organization and configuration, its operational principles and procedures, as well as communication protocols used.
The network architecture of the Internet is predominantly expressed by its use of the Internet protocol suite, rather than a specific model for interconnecting networks or nodes in the network, or the usage of specific types of hardware links.

